This is a long entry because I’m passionate about digital rights. Please take a moment to read. Thank you.
Imagine this: you run errands and come across a “magic” nightstand at your local department store. We’ll call said department store “Bigmart”. The magic part of the nightstand is that it transports a copy of whatever you put in that nightstand to a warehouse owned by Bigmart. The popular store chain is up front about how it works in that they own the warehouse, you don’t. The warehouse is secure and they claim they can’t see the contents of the warehouse, but they can unlock something if you lose your original copy and want to retrieve the latest copy of whatever was manually transported to the warehouse. They also let you know that because this warehouse can be used by thousands or millions of people, some of whom may not be the most morally grounded folks around, they’ll scan the contents from time to time to make sure you’re not doing anything illegal or shady with the contents you’re storing in their warehouse. They’re up front about all of this and you decide whether you want to put contents in the magic nightstand, knowing that whatever is transported to the warehouse plays by these rules.
Now, imagine Bigmart decides to change the rules. They have decided that in addition to scanning the copies that are magically transported to the warehouse, they’re also going to stop by your house every few hours and go looking through your nightstand. Now, they promise they’ll only look straight ahead when they enter your private dwelling and they will not look at anything other than the contents of the nightstand. They want to see what you have put in your nightstand for magic transport before it’s been actually transported to the warehouse.
Would you let the big company into your home and allow them to look at the contents of the nightstand? I can’t answer for you, but I will say that I would not allow this. I have no guarantee that Bigmart is looking at only the contents of the nightstand because I can’t see what they’re doing. I have to trust them, even after they’ve changed the rules of the transaction, because they use magic to transport and to get in and outside my house. I’m not allowed to see what they’re doing while they’re doing it.
Now, I know Bigmart is doing this for a good reason. They’re looking for nefarious material that could be harmful to other people, particularly children. They want to make sure I’m not using the magic nightstand to do illegal things. Instead of checking when these things arrive at the warehouse, they want to check before they get to the warehouse. And they don’t even have a list of what’s illegal, they’re just comparing the “fingerprint” of these things to a list of fingerprints. There’s one in a trillion chance the item’s fingerprint could wrongly match something on the list. They don’t even own the list. They’re just one of several companies that uses this third party list to check fingerprints.
I would still not allow Bigmart to come into my home and rifle through my nightstand, regardless of their intent. As an American, that feels a little too much like guilty before proven innocent to me, and while of course I don’t want anything illegal transported through my magic nightstand, they always said they would scan my stuff when it arrived at the warehouse, not come into my home and go through the nightstand first.
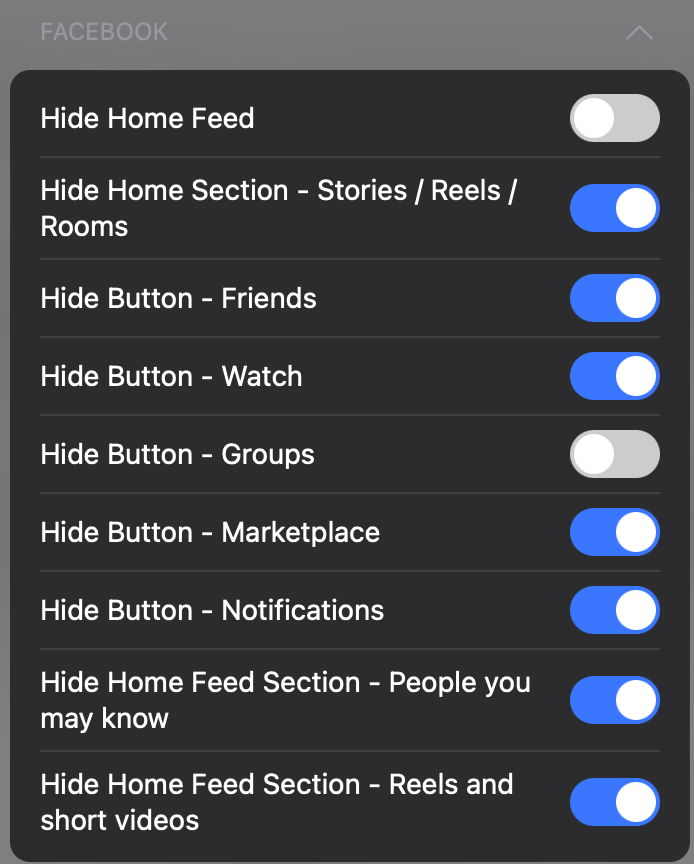
Apple announced they would start scanning photos destined for iCloud Photos (their cloud-based storage service) on each user’s iDevice (iPhone, iPad, etc) before it is uploaded to iCloud. This practice will begin in a future update. They’re doing this in the name of privacy and they’re doing this to save the children.
I’m all for saving children. This is a fact that is absolute, without question, and without hesitation. But I’m also really big on privacy. And scanning my files, even if they’re in a special bucket headed for iCloud, before they’ve actually arrived on the iCloud servers feels very creepy to this paranoid geek. Because Apple uses “closed source” software, meaning we can’t see how it works or when it’s doing these things, we the users have no idea as to what’s really happening. How do we know a cranky regime somewhere in the world isn’t going to add to the third party list of bad photos? Imagine if a dictator decided he or she (or they) wanted to know who has photos of adult, consenting, homosexual content on their phones? What if the FBI or CIA decided they didn’t want to limit the scanning of this nature to only photographs destined to be stored in iCloud? What if they wanted to see the contents of text messages or any other files on the user’s phone? What if someone hacks into your phone and puts something bad on it? The list can go on and on and on.
On the surface, Apple’s plans ding a person’s privacy quite a bit but when shrouded with the “but the children!” argument, users may not have a problem with the practice. I get that. But it’s a slippery slope. It’s a very slippery slope. And for years Apple has been selling their devices on the promise of them being the most privacy conscious company in tech.
It’s like they did a 180 overnight.
When we give up a little bit of privacy, we have the potential of giving up all of our privacy. We need to keep our children safe, no question.
But we need to keep our privacy safe as well.




 My brother-in-law owns a company that maintains gas pumps and associated equipment at service stations in the Pennsylvania-New Jersey area. During a recent visit he noticed a station down the street that had “canopy pumps”, where the mechanics of the fuel pump is incorporated into the supports that hold the canopy over the area, presumably to shelter customers from the elements while they’re filling their vehicles with explosive liquid. While here he didn’t get a chance to snap a photo of the pumps, but I told him I would stop by and do so. He’d use the information to research where the pumps were from and if his company could get access to them for his customers.
My brother-in-law owns a company that maintains gas pumps and associated equipment at service stations in the Pennsylvania-New Jersey area. During a recent visit he noticed a station down the street that had “canopy pumps”, where the mechanics of the fuel pump is incorporated into the supports that hold the canopy over the area, presumably to shelter customers from the elements while they’re filling their vehicles with explosive liquid. While here he didn’t get a chance to snap a photo of the pumps, but I told him I would stop by and do so. He’d use the information to research where the pumps were from and if his company could get access to them for his customers.