So this morning Apple released a security update for their latest version of macOS, called High Sierra. Earlier this year, macOS High Sierra was touted as being a new version of the operating system on Macs that would bring stability and a whole bunch of enhancements under the hood. The focus of High Sierra was to make its predecessor, macOS Sierra, better.
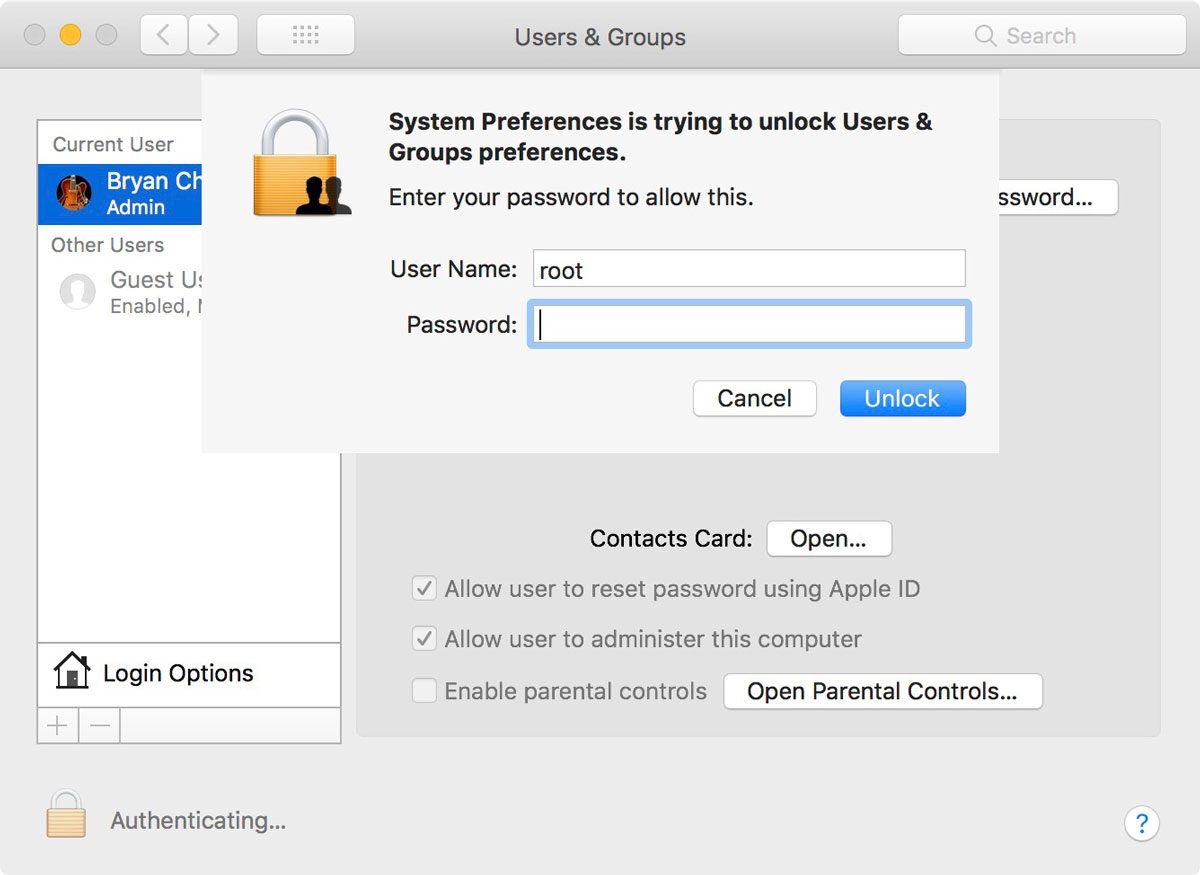
The purpose of today’s Security Update was to correct an issue that was announced throughout Social Media yesterday: that a user with physical access to a Mac was able to get to root user privileges, otherwise known as “Administrator” without using a password. Entering root as a username and then skipping the password prompt with a carriage return granted full access to the Mac. No password necessary. From there, anyone could do ANYTHING they wanted on the Mac: change usernames, delete everything, send out email, anything and everything is possible with root access to a Unix based machine.
To say that this was a security concern is a vast understatement. You wouldn’t be too far out of the realm of reality if you were to say that this was probably one of the biggest security blunders of the computer age.
The fact that this was pushed to production as part of the official version of macOS is mind boggling to me. Absolutely mind boggling.
Look, mistakes are made. I get that. As a software developer by trade I make mistakes all the time. My code is far from picture perfect and I’ve caused more than one user to scratch their head as software I’ve written has gone way off into the weeds due to simple bugs that I later squashed. The thing is, a lot of my bugs are found and corrected long before the software is released. That’s why we have things like UAT, or User Acceptance Testing. That’s why I spend hours testing and retesting my software before it even gets to UAT. To think that this sort of thing was missed by the macOS team at Apple, which one would presume is a large team at one of the largest corporations in the world, is mind boggling to me.
I’m impressed with how fast Apple pushed a patch to users. But honestly, I want more. I want to know how it happened, how secure the patch is and what the macOS team is going to do to avoid making a blunder of this magnitude again. This isn’t a matter of holding the Mac wrong or dropping a Mac from a ridiculous height and then claiming it can’t withstand the pressure, this is Security 101 on what is touted to be one of the strongest operating systems in the industry.
Apple dinged my faith and my trust in their software with this latest gaff. How do I know that my text messages aren’t going to start broadcasting to the wrong person? Where’s my guarantee that my data will always be encrypted and secure when bugs of this magnitude are starting to appear in their oldest operating system?
When a user pays a premium price for Apple’s products and services, they should never be expected to Expect Less. Mediocrity is not an option. Apple used to do better.
They need to prove that they can do better once again.
A M E N.